Our daily lives are more dependent on technology than ever before. That’s why cybersecurity is so critical.
Cyber threats are digital attacks aimed at accessing or changing data, stealing funds, disrupting business operations, and other harm.
A cyberattack may be as simple as an email that tricks a trusted employee into breaking security procedures. Or it could involve a network of computers under the control of a single attacker.
Malware
Malware, short for malicious software, are types of security threats that use programs to compromise computers and other devices. They can steal or delete files, change a device’s functions, or spy on your activities. They can spread from device to device or stay on one computer, but they all work similarly: exploiting vulnerabilities to steal sensitive information and disrupt your systems.
Viruses are malware that piggybacks on other programs to replicate, infecting them with their code and then spreading those programs from one system to another. Worms, on the other hand, can self-replicate without attaching to existing programs or modifying data. They use security vulnerabilities to spread and go unnoticed until they reach a critical mass and consume too much of a network’s resources or hard disk space.
Attackers can also use malware to extort money from victims. Ransomware is a typical example, where attackers encrypt a victim’s files or device and demand payment for the decryption key. Other attacks can exploit weaknesses in networks and devices to gain unauthorized access, like a SQL injection attack. Lastly, an attacker can impersonate others to achieve their credentials, like passwords or PINs, in a social engineering technique known as a phishing attack.
Viruses
Like biological viruses, computer viruses can replicate to attack multiple devices. They can corrupt data, reformat hard disks and steal information. They can also hide on a machine and remain undetected. These attacks are categorized as malware, and the threat is constantly evolving.
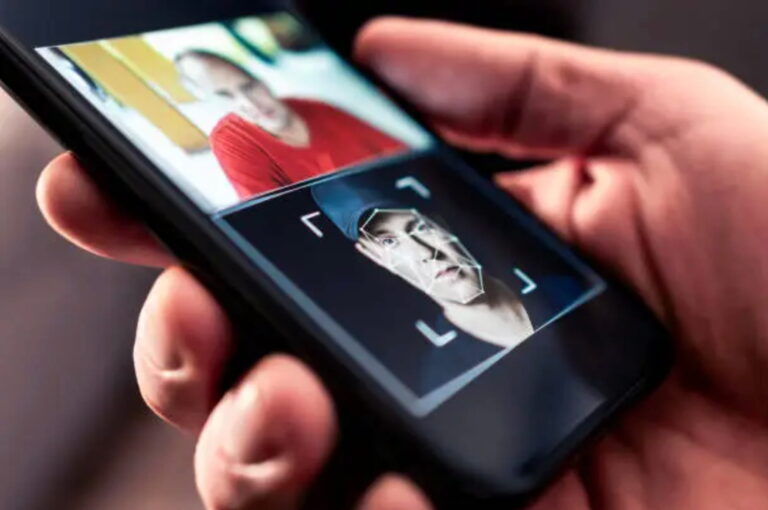
Spyware is another typical cyberattack that violates privacy. It can collect passwords, credit card numbers, and other sensitive information or snoop on communications using the mobile device’s microphone and camera features. Anti-spyware programs are commonly included in major antivirus packages.
Hackers use phishing techniques to send fake email messages that trick the victim into clicking on malicious links or entering their credentials into fraudulent websites. These hacks can lead to the theft of PII, financial fraud, and identity theft. Services like MailSpec will prevent phishing attacks and protect your data using encryption to secure private information.
A man-in-the-middle attack (MITM) involves hackers intercepting communication between two parties to spy on victims or change the message. This severe attack is less common nowadays since most email and chat systems now offer end-to-end encryption, preventing attackers from tampering with conversations.
Worms
Worms are malware replicating itself, consuming bandwidth and hard-drive space while undermining device and network performance. When a worm gains access to a machine, it can corrupt or delete files and steal data. It can also cause many other problems, such as crashing systems or causing unauthorized access to systems.
Like viruses, worms are designed to slip through holes in security software and operating system components. They use a variety of techniques to spread, including email attachments, instant messaging worms, file-sharing worms, and Internet worms. Many worms are programmed to look for vulnerabilities and exploit them, but some are designed to avoid these systems.
The most common way a worm can be detected is by monitoring unusual network or system activity. When a worm is active, it will attempt to connect to more hosts than would be typical for non-infected systems. This increase in attempted connections should be noticeable and warrant further investigation. It’s also essential to keep staff trained on cybersecurity threats and share that information with your team, mainly if they work remotely or with external clients. This can help reduce the likelihood of a worm attack and help your teams respond quickly to any attacks.
Botnets
Cybercriminals use bots to compromise computers and other devices connected to the internet. This malware silently installs itself on your device, and it can lay dormant for months or even years until the attacker is ready to activate it for their nefarious purposes.
Depending on its purpose, the malware may harvest data by capturing keystrokes to steal passwords or credit card information. It may also deliver phishing attacks, spam campaigns or click fraud, distribute malware, or conduct DDoS attacks.
A botnet comprises tens of thousands of infected computers or devices and is usually controlled by a malicious actor called a bot herder. These herders exploit various methods to infect the devices, including phishing attacks, software and website vulnerabilities, and hardware supply chain weaknesses.
Bot herders can co-opt devices such as routers, servers, and smartphones to form massive botnets for cyberattacks. When these devices are part of a more extensive network of compromised machines, it becomes easy for bad actors to launch large-scale distributed denial of service (DDoS) attacks.
Man-in-the-Middle Attacks
Man-in-the-Middle attacks allow criminals to intercept and eavesdrop on data communication between parties, such as login information or credit card details. These cyberattacks use a process known as data interception and decryption, and they are common when users access websites via public Wi-Fi networks or non-secure private connections.
Attackers begin by sniffing sensitive information through tools that inspect packets — units of data sent over networks — looking for unencrypted communications or connection vulnerabilities. They can also employ techniques like source-routed IP packets and HTTP cookie hijacking. A cybercriminal retrieves a victim’s session token from a simple website by redirecting them to a fake one that mimics the site.
Once attackers have access to user information, they can use it to breach accounts, steal funds or make unauthorized purchases. They can also use this information to launch more long-term, advanced persistent threats within an organization by gaining the credentials to mine company data or disrupt production environments.
The best way to protect against man-in-the-middle attacks is by using a certificate management system that verifies email authenticity with encrypted connections. Additionally, ensuring that all web servers are configured only to use HTTPS can help prevent attackers from intercepting communications and redirecting users to fake sites.